How would you improve your security if you could anticipate attacks rather than just react to them?
Do you know how long it takes to detect and mitigate a critical vulnerability in your organisation?
Is your company really protected against the latest advanced threats?
If you have doubted the answer or are simply not sure if you can answer these questions, I invite you to read on. Today, there are tools that can help you improve your organisation's cybersecurity posture thanks to Artificial Intelligence (AI).
New cyber threats emerge every day; they are constantly evolving. There is a great need for organisations to adopt strategies that enable them to not only detect and respond to incidents, but also to ahead of time to them.
In this context, a tool for Continuous Irrigation Exposure Management –Continuous Threat Exposure Management (CTEM)-has become a key player for companies seeking to strengthening its security posture.
From a CISO's point of view, the adoption of a CTEM not only enhances the visibility of vulnerabilities in the attack surface, but also allows for an intelligent prioritisation and a effective correction. It is not the same to know that there are N vulnerabilities in our company as it is to really know how the one that could do us the most harm if exploited could affect us.
The advantages of having a CTEM can be summarised in five points:
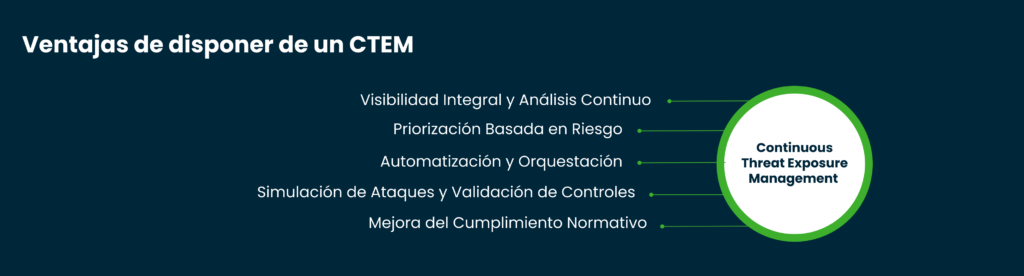
- Integrated Visibility and Continuous Analysis
Traditional vulnerability management relies on periodic scans, which creates windows of exposure. A CTEM operates from on an ongoing basisassessing the real-time security posture and providing relevant information on active and potential threats. - Risk Based Prioritisation
Not all vulnerabilities represent the same level of risk. A CTEM employs advanced models of contextualised riskThe exploitability of a vulnerability is aligned with the criticality of the affected asset, which helps improve decision making. - Automation and Orchestration
An effective CTEM must be integrated with SOAR (Security Orchestration, Automation and Response) tools in order to automate mitigation of threats in real time, speeding up their resolution. - Attack Simulation and Control Validation
There are solutions for Breach & Attack Simulation (BAS) that allow validate the effectiveness of defences through controlled simulations of attacks. This helps companies to optimise your defensive strategies without waiting for a real incident to occur. - Improving Regulatory Compliance
Regulations such as NIST, ISO 27001, and frameworks and MITRE ATT&CK emphasise the importance of continuous threat exposure management. A CTEM facilitates the regulatory compliance by providing tangible evidence of continuous risk assessment and mitigation.
The CTEM is therefore much more than an attack simulator. It must offer a holistic view of our cyber security posture and integrate easily with the ecosystem of the different manufacturers we already use in our corporate environment, as well as facilitating automation as far as possible.
Only then can it provide the CISO and the cybersecurity team with the KPIs necessary for a effective management of cyber security in your organisation.
At Ukotek we were pioneers in Spain when we decided to offer a Managed Continuous Risk Exposure Service to our clients. After an exhaustive analysis of various technologies, we can now say that we were right to make a firm commitment to PICUS Security.
We find it very gratifying to observe the initial surprise of our interlocutors at the end of the classic initial proof of concept (POC), and the satisfaction with the results obtained once they have contracted the service and become Clients.
In addition to the aforementioned advantages of having a CTEM, our clients highlight five aspects of our service that make us stand out from the rest. PICUS Security:
- The ease of integration -in a matter of minutes - with SIEMs such as Splunk.
- The speed of delivery, without agents and without the need to operate other equipment.
- The capacity to empowering the SOCThe use of the rules, with concrete use cases, or question it on the basis of the effectiveness of the established rules.
- A bookshops of threats updated daily
- The continuous support of a Client Success Manager
In short, implementing a CTEM is not just a security strategy, but a competitive advantage. By reducing threat exposure, improving visibility and optimising incident response, organisations can operate with greater confidence in an increasingly hostile digital environment.
Leading manufacturers, such as PICUS Securitycontinue to innovate, enabling businesses to adapt and strengthen their resilience to emerging threats.
If you're looking for a solution that is easy to implement and integrates with your SIEM, it's time to take the next step and strengthening your security posture with Ukotek and a first class CTEM.