Advanced Cybersecurity Solutions
We are partners with high value-added cyber security providers.
The level of cyber security maturity varies with each company, its resources and its business objectives. The diversity of vendors and technologies, coupled with a shortage of skilled resources, can make it difficult to know where to start.
At UKOTEK, we understand the challenges of cyber security and specialise in providing innovative and advanced solutions, tailored to your specific needs.
We offer a full range of services designed to protect your business in a comprehensive manner. The following are our main services:
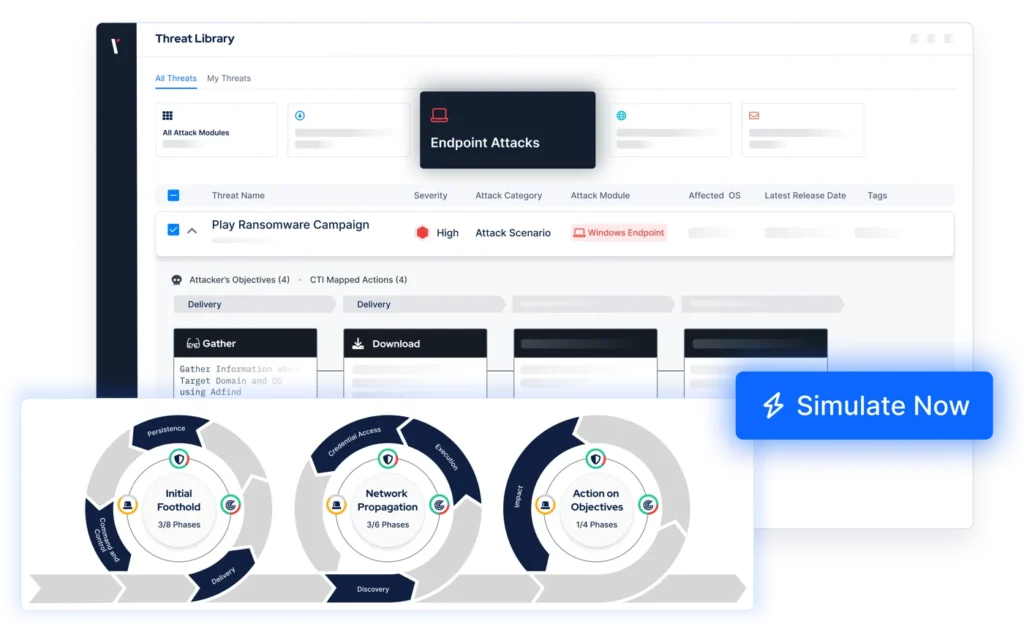
Continuous Risk Exposure Management (CTEM)
Can you be sure which threats pose the greatest risk to your organisation?
We offer an innovative cyber-attack simulation platform that enables organisations to continuously assess and improve their security posture. By emulating the latest advanced attack techniques, including ransomware and advanced persistent threats (APTs), Picus Security identifies vulnerabilities and provides targeted recommendations to strengthen security defences, ensuring that businesses are always one step ahead of cybercriminals.
Now you will be able to know, on a regular and even automated basis, the detection and protection capacity of all your company's cybersecurity tools, allowing you to prioritise investments to focus on what is really important
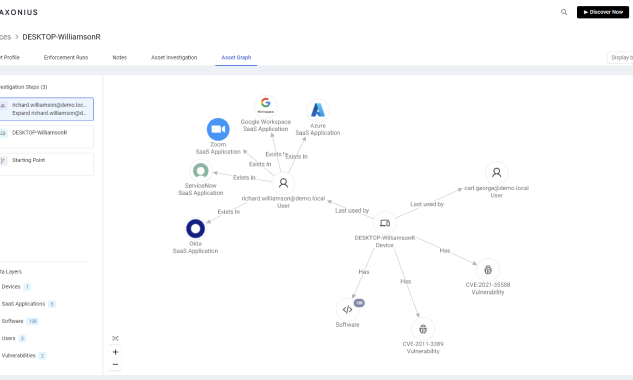
Complete visibility of your assets in one click with Axonius
Do you have full visibility of the configuration and status of all devices?
Axonius is a comprehensive cyber asset management platform that helps organisations identify, manage and secure all their digital assets in complex environments. Seamlessly integrating with more than 1150 IT and security data sources, the Axonius platform becomes a true system of record for digital infrastructure, including hardware, software, SaaS applications, cloud, user identities and more.
If an attacker compromises the Active Directory, they can gain privileged access to the entire IT infrastructure, allowing data theft, disruption of operations and the spread of malware.
Semperis ensures that backups are always clean of malware, facilitating fast and secure recovery in the event of an incident, and eliminating compromise.
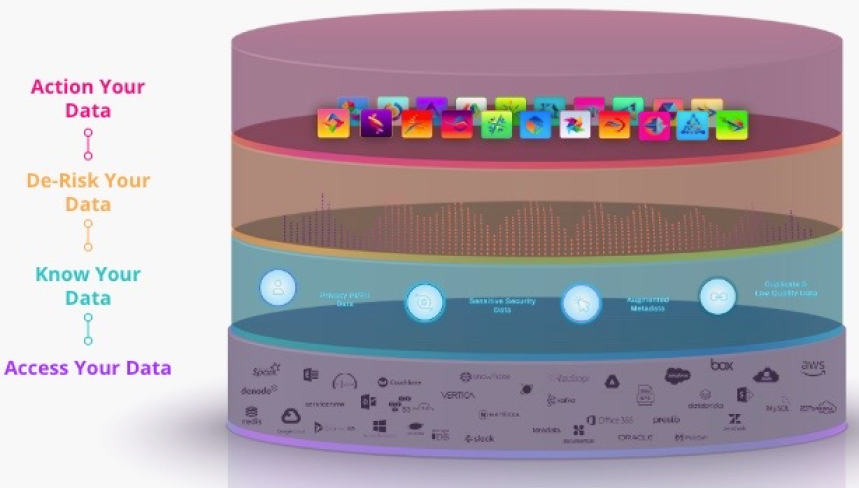
Discover, classify and protect your data with BigID
BigID is an innovative platform designed to provide full visibility, advanced classification and automated protection of sensitive and regulated data in any business environment. With a focus on data security and compliance, BigID enables organisations to efficiently discover, catalogue and manage their data, including ensuring protection against unauthorised access and compliance with global regulations.
It is crucial to have constant monitoring that provides full visibility of all assets and external providers. This not only prevents risks, but also ensures compliance with regulations such as PCI DSS 4.0, without complicated integration processes.
Protect your site and ensure that all suppliers operate securely and to the highest standards.
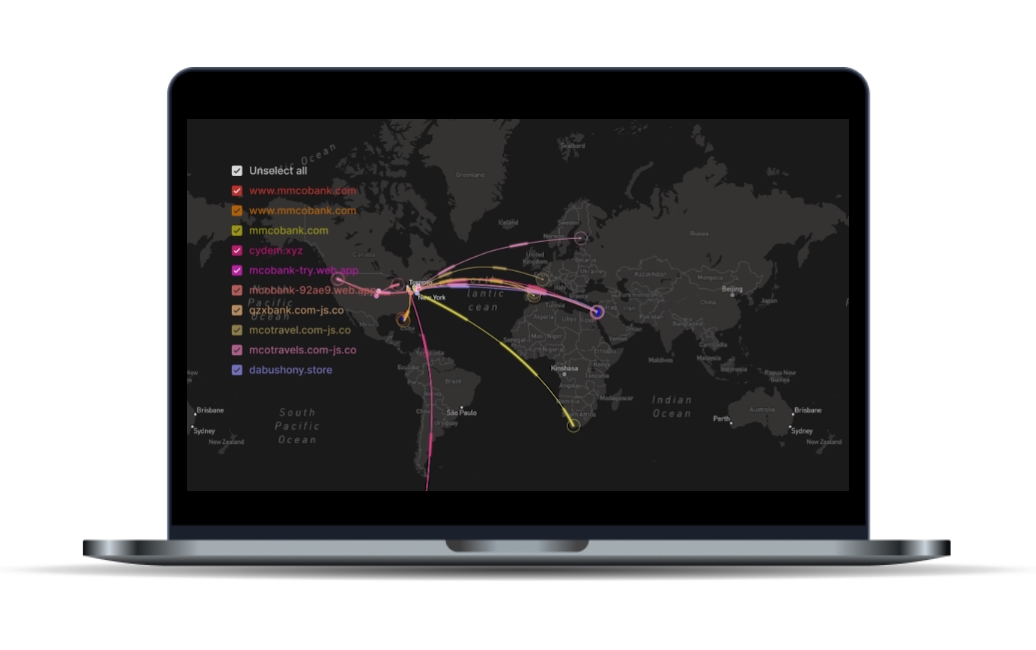
Web spoofing protection
Web phishing occurs when malicious actors create fake websites that mimic your company in order to deceive your customers and steal confidential information.
Brand hijacking, on the other hand, involves the unauthorised use of your brand for fraudulent activities, damaging your reputation and the trust of your customers.
These attacks can have devastating consequences, including financial loss, reputational damage and loss of customer confidence.
It is essential to implement proactive measures to detect and prevent these threats before they cause harm.
We offer a comprehensive solution to prevent identity theft and brand hijacking.
Our advanced technology continuously monitors the web to detect any attempt to impersonate or misuse your brand.
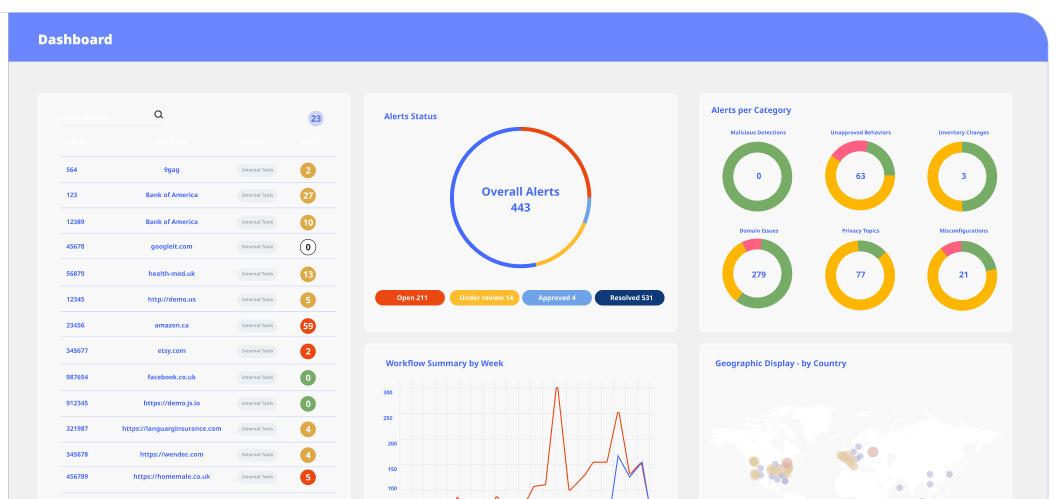
PCI DSS 4.0 compliance
Today's websites rely on multiple third-party services that, while enhancing their functionality, also increase security risks. These components, invisible to traditional controls, can be a gateway for threats such as web skimming or malware.
It is crucial to have constant monitoring that provides full visibility of all assets and external providers. This not only prevents risks, but also ensures compliance with regulations such as PCI DSS 4.0, without complicated integration processes.
Protect your site and ensure that all suppliers operate securely and to the highest standards.
We offer global and scalable solutions
Identity-based protection (ITDR) and AD recovery
Did you know that 82% of all attacks on companies target AD?
Semperis is a leading identity protection and disaster recovery solution for Active Directory environments. Designed to prevent, mitigate and remediate cyber-attacks, Semperis offers comprehensive identity protection, ensuring that critical IT infrastructures are resilient against the latest threats.
If an attacker compromises the Active Directory, they can gain privileged access to the entire IT infrastructure, allowing data theft, disruption of operations and the spread of malware.
Semperis ensures that backups are always clean of malware, facilitating fast and secure recovery in the event of an incident, and eliminating compromise.

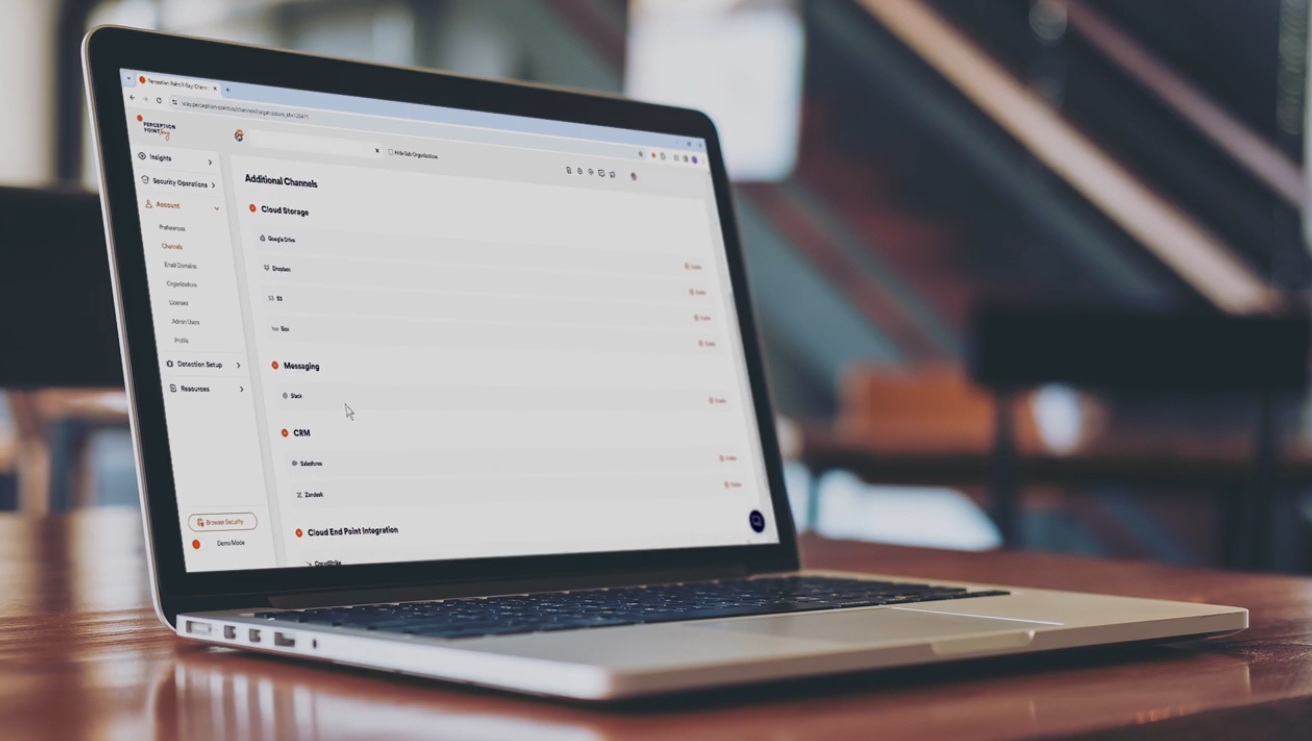
Proactive protection of the working environment
Content-based attacks are cyberthreats that infiltrate through files, emails, messaging applications and other digital media that organisations use on a daily basis.
These attacks can include malware, ransomware, phishing and other malicious tactics that exploit documents, images and links to compromise your network security and steal sensitive data.
We offer 360-degree protection against any type of content-based attack, ensuring that all collaboration channels are secure. Our solution analyses and stops threats in real time, providing an effective barrier against the most sophisticated tactics of cybercriminals.
If an attacker compromises the Active Directory, they can gain privileged access to the entire IT infrastructure, allowing data theft, disruption of operations and the spread of malware.
Semperis ensures that backups are always clean of malware, facilitating fast and secure recovery in the event of an incident, and eliminating compromise.
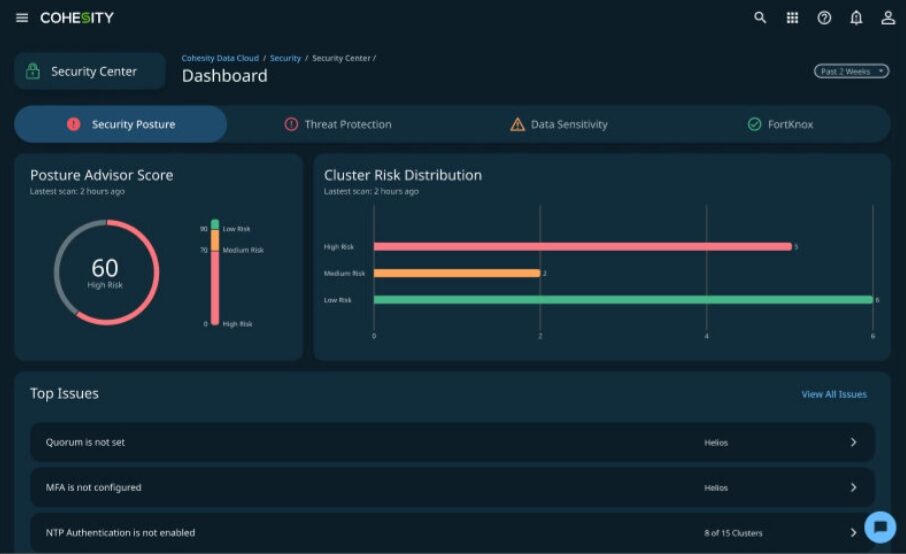
Advanced and immutable data protection
In an increasingly complex digital environment, protecting critical areas is essential to the security of your organisation. Critical areas include endpoints (end-user devices), cloud workloads, digital identities and sensitive data. These areas are the most vulnerable and therefore the most targeted by cybercriminals. A security breach at any of these points can result in serious security breaches, data loss and reputational damage.
To address these challenges, we offer a leading cyber security solution that protects the most critical risk areas of your organisation.