Standards, regulation and compliance
We are certified experts for obtaining certificates and compliance with regulations.
We help our clients to implement best practices in cybersecurity, promoting the adoption of a Zero Trust strategy according to the frameworks promoted by the American National Institute of Standards and Technology (NIST). We advise you on how to obtain 27001 certification from the International Organization for Standardization (ISO) and compliance with European and International Regulations.

Our team of auditors and consultants has extensive experience in the implementation of ENS, DORA, NIS2 and ISO 27001.
All of them have the accreditations - CCN_CERT/ENS, CISA, ISO/IEC 27001:2013 - that allow us to accompany your company in the certification process.
ENS and NIS2 compliance
We implement the National Security Scheme (ENS) and NIS2 and accompany our clients in the certification process and subsequent advice.
Certified audit team
We have an expert team of auditors with the following international certifications:
- ISO 27001 Auditors
- Certified Information Security Officer (CISA)
PCI DSS 4.0 compliance
We offer a managed service to provide full visibility of the risks associated with third parties. If you sell services through your website, you will be able to respond to the new PCI DSS 4.0 requirements.
ENS - National Security Scheme
For whom?
The ENS establishes the minimum cybersecurity requirements to be met by public sector entities, their technology providers, and companies wishing to align themselves with the high security standards demanded by the Public Administration in the protection of their systems and data.
What for?
It aims to ensure the confidentiality, integrity, availability and traceability of data and services, reducing the risks of cyber-attacks and other digital threats.
How?
To comply with the ENS, organisations must conduct an initial assessment to determine their level of security, implement appropriate measures, and conduct regular audits and reviews to ensure ongoing compliance. This process not only improves security, but also builds trust in public services.




Need help?
Our certified auditors ensure compliance with the National Security Scheme (ENS), providing expert advice and certification to protect your organisation.
NIS2 - Network and Information Systems Security Directive
For whom?
The NIS2 Directive focuses on public and private entities in critical sectors such as energy, health, banking, and essential digital services, as well as medium and large enterprises, to strengthen cybersecurity and incident response in the European Union.

What for?
It aims to improve cyber security and information systems in the European Union. It seeks to ensure a high common level of cyber security, strengthen the resilience of critical infrastructures and reduce the vulnerability of these systems to cyber attacks.
How?
Key requirements of NIS2 include risk management, incident reporting and the implementation of technical and organisational security measures. Organisations must identify their critical assets, implement adequate security controls and maintain continuous monitoring to detect and respond to incidents.
Do you want to start your certification process now?
Trust our certified auditors to comply with the NIS2 Directive, offering you expert advice and certification to improve the cyber security of your infrastructure.
Cybersecurity Framework Guidance: ISO 27001 and NIST
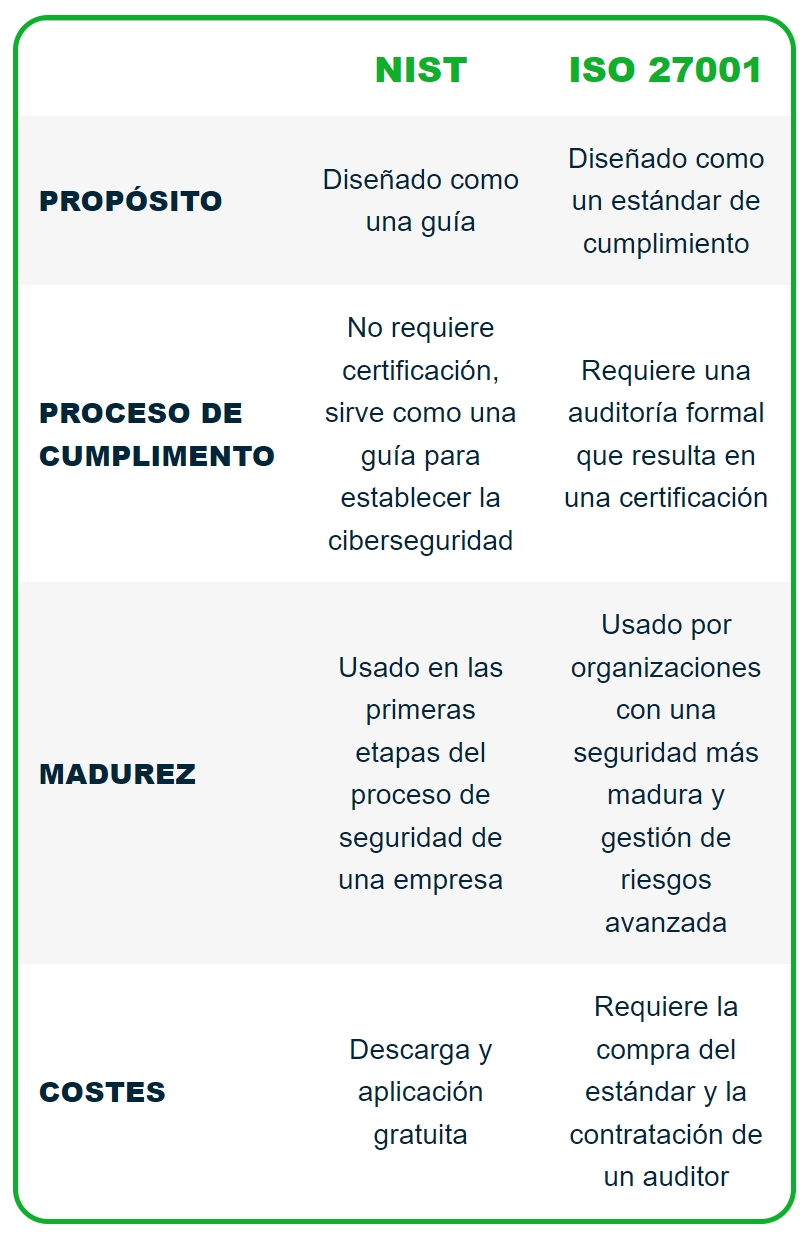
Cybersecurity frameworks such as ISO 27001 and NIST provide essential guidelines to help organisations comply with security regulations.
ISO 27001 focuses on information security management through a comprehensive management system.
NIST provides technical and organisational guidelines to improve cyber security.
Implementing these frameworks involves establishing clear security policies, conducting regular risk assessments and adopting appropriate security measures. These frameworks not only help to comply with ENS and NIS2, but also strengthen the organisation's overall cybersecurity posture.
| NIST | ISO 27001 | |
|---|---|---|
| PURPOSE | Designed as a guide | Designed as a compliance standard |
| COMPLIANCE PROCESS | No certification required, serves as a guide to establishing cybersecurity | Requires a formal audit resulting in certification |
| MATURITY | Used in the early stages of a company's security process | Used by organisations with more mature security and advanced risk management |
| COSTS | Free download and application | Requires the purchase of the standard and the hiring of an auditor. |
Security Strategy Zero Trust
The Zero Trust security strategy is based on the premise that nothing, inside or outside the network, should be trusted without continuous verification. The core principles of Zero Trust include constant verification of users and devices and risk-based access control.
To implement a Zero Trust strategy, organisations must conduct a risk assessment, segment their network to limit access and continuously monitor all activities. This strategy is essential to protect data in an environment where threats can emerge both internally and externally.
