Tell him goodbye at umbrellas, go out the sun
How do you prevent what is meant to come from not coming? The best way to avoid impact is to get ahead of it. To do this, we need a security strategy proactivenot only reactive.
The first step in anticipation is to understand how the attacker operates. Because if there is one thing that characterises cybercriminals, it is their persistence. The data confirms it: more than 200,000 domains are created every day, and the number of new domains is 85% has malicious purposes. In addition, the 92% of the malware relies on DNS to deploy its attacks. Doing the numbers, this means that two domains are born every second designed to attack. And, of course, any of them can target your company.
If we analyse the most used domains, we find a surprise: the most registered TLD no is neither .com nor .net, but .tk, a domain associated with Tokelau, a small self-governing territory in New Zealand with a population of just 1,400. A curious but revealing fact: cybercriminals take advantage of poorly controlled domains to launch attacks such as the IDN homographby spoofing legitimate URLs with similar characters, which are difficult even for machines to detect.
The limitation of traditional solutions
Until now, the traditional approach has been to protect the DNS with blacklists of known malicious domains. But there is an obvious problem: if 30 new domains have been created in the last minute for illegitimate purposes, How can a static list identify them in time?
It simply cannot.
Most of the solutions on the market follow a model of detection and response. However, if we really want to stay ahead of the attacker, we need to understand their strategy. and anticipate their movements.
A smart strategy: early detection with AI
The attacker often throws a stone and hides his hand, so he uses a TDS (Traffic Distribution System) to distribute its malicious content over the network, but it stipulates that it does so under certain conditions. In other words, it gets the malware only in the case where the victim is of interest to them.
In five of the seven steps of the Cyber Kill Chainthe attacker needs to use DNS. Why not turn it into a strategic control point? That's where Threat Defence from Infoblox.
Thanks to artificial intelligence and machine learning, this solution does not only detect malware before it is activatedInstead, it identifies suspicious patterns of behaviour in real time. Instead of relying exclusively on blacklists, parses the 100% of DNS traffic -both incoming and outgoing- blocking threats before they become a problem.
For example, when an attacker registers a domain just before an attack or reactivates an old domain in order to go unnoticed, Infoblox Threat Defence detects it almost in zero time. With only one 0,002% of false positivesAI makes it possible to anticipate emerging malicious domains with unprecedented accuracy.
In addition, the solution identifies fake domains or "lookalikes used in fraud, through a massive daily analysis of DNS patterns.
Real impact on your organisation
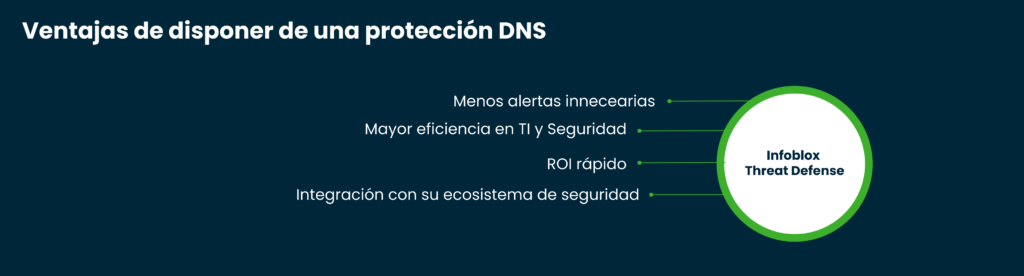
Adopt Infoblox Threat Defense not only improves security, but also optimises the operation of your team:
- Fewer unnecessary alerts: Reduces up to a 40% EDR notifications.
- Increased IT efficiency and security: Automates detection and response, reducing human error.
- Rapid ROI: In most cases, the return on investment is less than six months.
- Integration with your security ecosystem: Reduces the load on firewalls, proxies and IPS, improving your overall performance.
At UkotekWe are committed to innovative solutions that strengthen the cybersecurity of your company, improving operational efficiency and reducing costs.
So the question is not whether you will need to reinforce a proactive strategy, but when. And the best answer is before it is too late. Anticipate. With solutions that bring intelligence. That is the question.
Do you want to know more? Contact us at and find out how we can help you strengthen the security of your organisation.